Public vs. Private Key Encryption
With an explanation that you'll never forget.
I bet that multilinguals will find the cryptography behind bitcoin (public key encryption) intuitive. Here’s the difference between private and public key encryption explained in a way that you’ll never forget.
Private Key Encryption
Everyone has probably used private key (or more accurately symmetric) encryption as a kid. You want to send a message to someone else, so you encrypt it with a specific key shared only with the intended recipient of your message. If someone other than the intended recipient gets the key, the message is compromised.
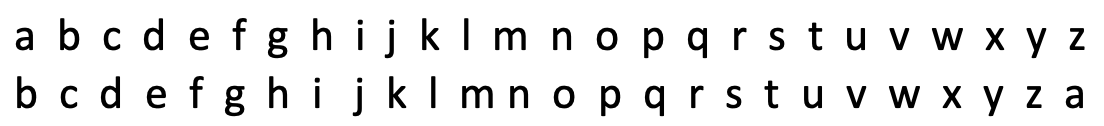
One super simple one is to swap every letter used in a word for the next one. D-o-g becomes e-p-h (extra brownie points if you tell me what this means: Zpv bduvbmmz efdszqufe uijt! Lvept up zpv boe zpvs joufmmjhfodf)
As long as you share how you encrypted the word (called “the key”) with the person you want to send the message to, you can communicate with each other. However, the message recipient must know the key to the message to decrypt it. And that’s the limitation of private key encryption.
Public Key Encryption
Public key encryption fixes this. Instead of giving your recipient a private key, everyone instead has a public key that they broadcast widely. When you want to send someone a message, you use *their* public key to encrypt your message. Then you broadcast the encrypted message to everyone. Only the person with the private key for the public key you used to encrypt the message can decrypt the message.
It’s a lot like speaking to someone in a rare language like Ubuntu while in public. Everyone can *hear* what you’re saying, but only your friend will be able to *understand* what you’ve actually said. Knowledge of Ubuntu is the private key and the sound of your speech is the encrypted message. Everyone has access to the sounds of your message, but very few people have the knowledge of Ubuntu necessary to decrypt the sounds.
Flaws
There are a few flaws in this model for public key encryption.
For one, a message in another language can be understood by anyone else who speaks the language. Nobody walks around with a pop-up that says what languages they can understand. And thus, your conversation in Spanish or Hindi with your friend may be understood by an eavesdropper. This doesn’t happen with public key cryptography because only one person can decrypt your message - the one with the private key.
The second issue is that your friend can respond to you speaking Ubuntu in Ubuntu. It’s a two way street because you both are using the same language. But public key encryption is different because it’s not a two way street. Your public key is not the same as someone else’s public key. They are different. Perhaps it would be more accurate to say that a speaker of the Italian dialect from Venice can understand the Italian dialect of someone from Genoa, but they cannot speak the other’s dialect.
The third and final issue with the second-language analogy is that you actually use someone else’s public key to encrypt your message. They use their private key to decrypt it. It wouldn’t be like speaking different dialects, it would be speaking your counterpart’s dialect, and him speaking yours! Public keys encrypt, private keys decrypt.
With all this being said, the benefit to this model of public key encryption is that everyone knows what it’s like to be in a room with people speaking another language. The message may be public, but it’s “encrypted,” and thus, it’s private. That’s what makes it easy to remember.
Relevance
Bitcoin and other cryptocurrencies use public key encryption to send and receive money. Everybody with bitcoin has a public wallet address, to which you can send crypto at any time. But only the person with the private key for that address can access the funds in that crypto.
Public key encryption was invented publicly in 1976 when American cryptographers Whitfield Diffie and Martin Hellman published New Directions in Cryptography, an 11 page paper that goes into the public-private divide in much detail.